Update — May 6, 2026 (evening): This matter is now in litigation. Bowman v. Amazon.com Services LLC, Volusia County, Florida, Case No. 2026 17782 COCI. Pretrial conference set for August 11, 2026. Summons issued. See update log at the end of this article.
Update — May 8, 2026: Amazon blocked my one-star review of this listing. The review (Amazon Reference R9NRAS3H4BZB8, submitted 5/8/2026 at 9:24 AM ET, titled “Spyware or Adware Injected In laptop”) stated that the laptop had spyware/adware preinstalled, that the install sequence was visible in PowerShell, and that I had filed a formal complaint and was consulting an attorney. Amazon’s stated reason: the review “doesn’t meet our community guidelines.” Amazon will not let me warn other shoppers about this seller through their own review system. The takedown email is preserved as evidence.
I bought a “Renewed” Dell Latitude 7420 from Amazon. Three days after I powered it on, a popup hit my screen telling me to “Choose a recommended antivirus” — branded PC App Store, a documented adware family.
That popup is what kicked off the forensic work. What I found is the kind of thing Amazon’s Renewed program standards explicitly forbid. Allegedly preinstalled adware. Allegedly preinstalled residential-proxy software. A 21-minute manual install sequence sitting in the laptop’s own Prefetch directory — recorded 82 days before I logged in for the first time.
Independently confirmed by Malwarebytes: 15 threats across three unwanted-program families.
Here’s everything, with the receipts.
What I bought
May 1, 2026: Dell Latitude 7420 Business Laptop, Amazon Renewed program. 11th Gen i7-1185G7, 32GB RAM, 512GB SSD, Windows 11 Pro. $489.89 total. Delivered to my front door in Port Orange, Florida on May 3.
Sold and shipped by a third-party seller: ElectronicsBazaar Store, a doing-business-as name for Kay Kay Overseas Corporation.
I powered it on the evening of delivery, set up my Microsoft account, installed my normal tools, and got to work. Standard new-laptop-day routine.
What I found three days later
May 6, 4:30 AM. The laptop had been running overnight. I came back to this on my screen:
“Choose a recommended antivirus to secure your data.” Powered by PC App Store™.
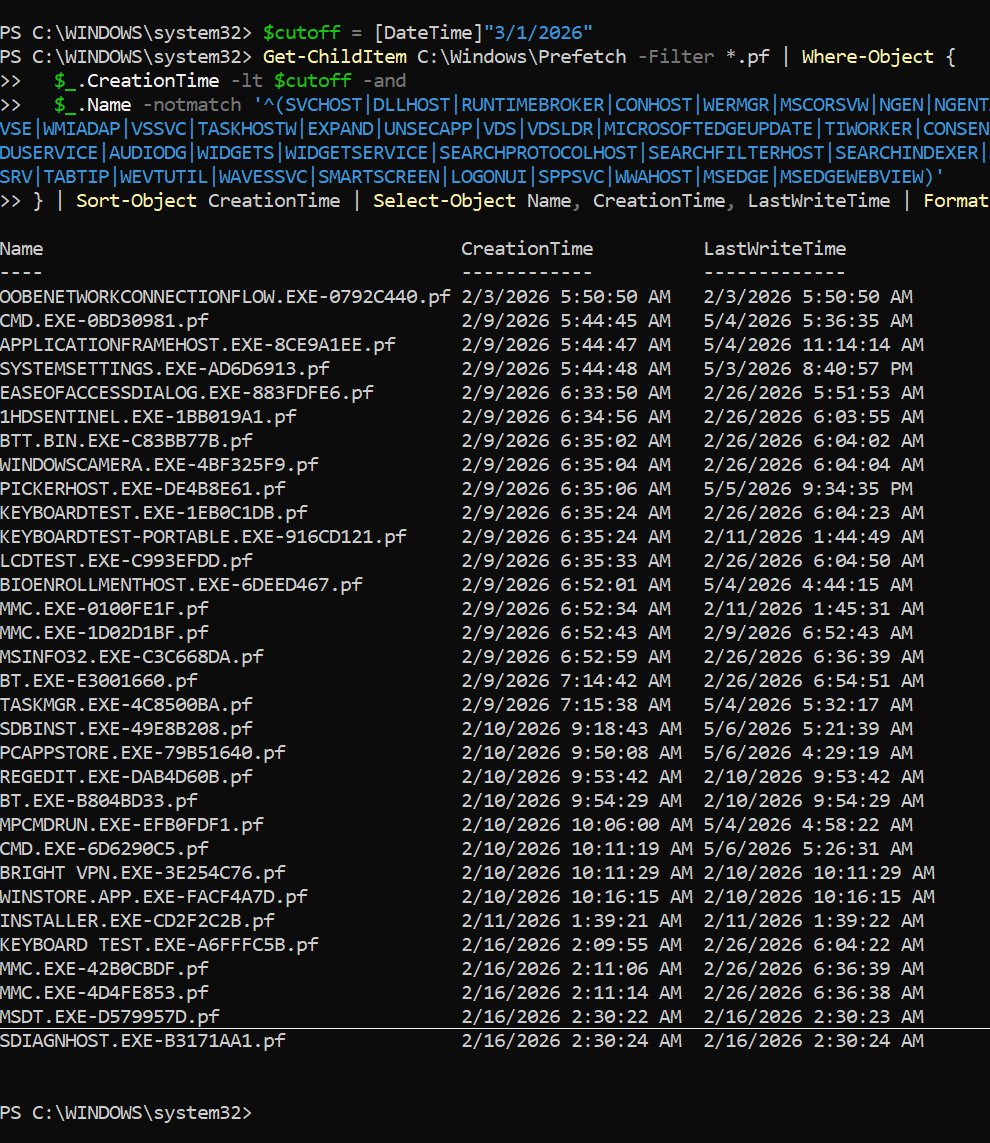
I’ve been doing web work since 2009. I know what scareware looks like. I know I didn’t install PC App Store. So I pulled the Prefetch directory — C:\Windows\Prefetch — which logs the first time every executable runs on a Windows install. Prefetch is forensic gold. It can’t be easily faked, it’s enabled by default, and it survives unless someone wipes it. The seller didn’t wipe it.
Here’s the timeline:
| Date | Time | Event |
|---|---|---|
| 2/3/2026 | 5:50 AM | Fresh Windows install completed |
| 2/9/2026 | 5:39 AM – 7:16 AM | Hardware QA tools run |
| 2/9/2026 | 8:24 AM | Bright VPN and BrightData folders created |
| 2/10/2026 | 9:50:08 AM | PCAPPSTORE.EXE first execution |
| 2/10/2026 | 9:53:42 AM | REGEDIT.EXE opened — manual registry editing |
| 2/10/2026 | 10:11:19 AM | CMD.EXE opened — manual command prompt |
| 2/10/2026 | 10:11:29 AM | BRIGHT VPN.EXE first execution |
| 2/16 + 2/26/2026 | — | Additional QA passes |
| 5/3/2026 | 8:01:10 PM | My first logon |
| 5/6/2026 | 3:29 AM | UPDATER runs silently while laptop in standby |
| 5/6/2026 | 4:29 AM | PCAPPSTORE.EXE last execution — scareware popup to me |
Read it carefully. Feb 10, 9:50 AM: PC App Store runs for the first time. Feb 10, 10:11 AM: Bright VPN runs for the first time. That’s 21 minutes apart. REGEDIT and CMD got opened in between.
Someone sat at this laptop, ran an adware installer, opened the registry editor, opened a command prompt, and ran a residential-proxy installer. By hand. In sequence. On a clean OS that the same seller had installed exactly seven days earlier.
I didn’t power it on for the first time until May 3, 8:01 PM. That’s 82 days later.
What was actually installed
PC App Store — a documented adware family with industry signatures from Trend Micro, Malwarebytes (PUP.Optional.PCAppStore), and BleepingComputer. Documented behaviors include scareware popups (the one I got), browser-search hijacking, scheduled-task persistence, and telemetry exfiltration.
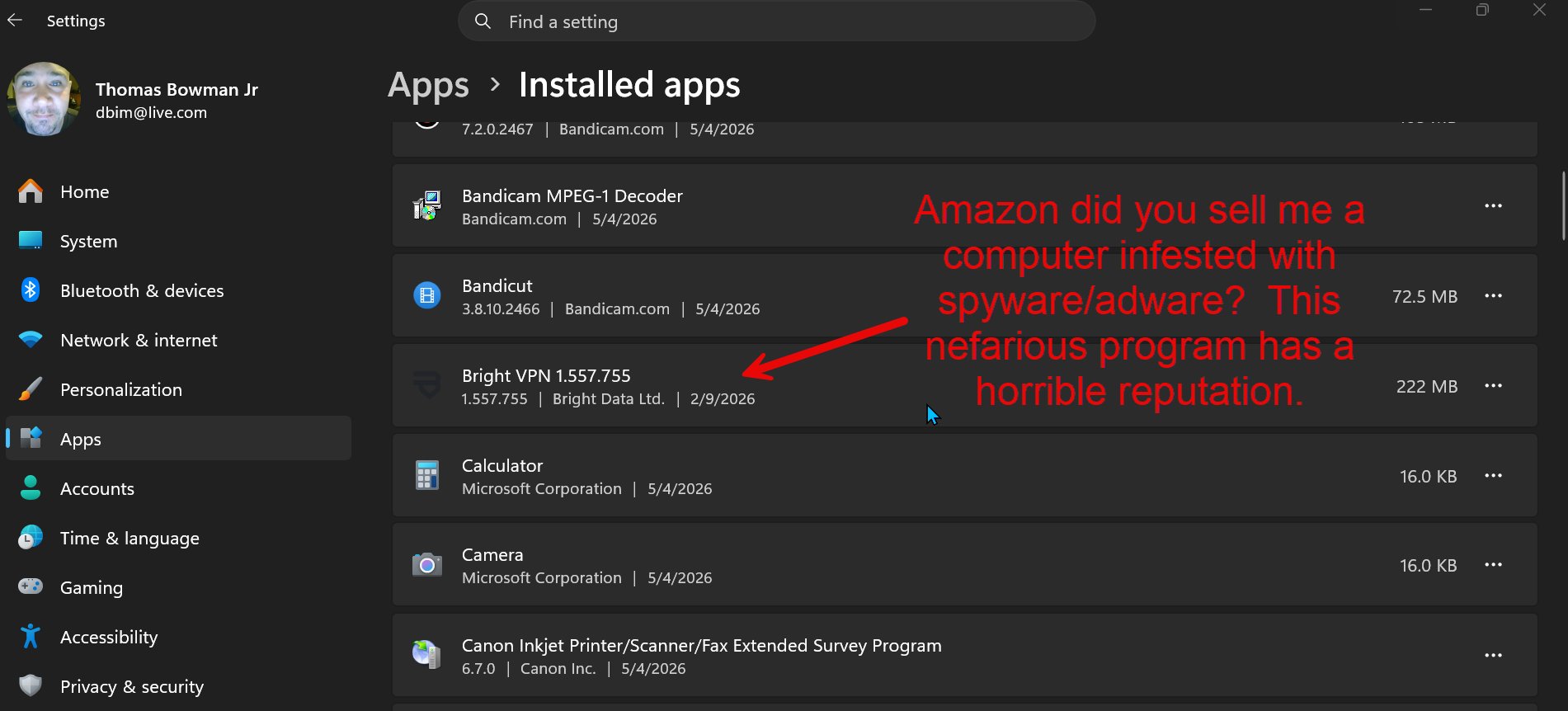
Bright VPN — this one’s worse. Bright VPN is a product of Bright Data Ltd., the parent company of Hola VPN — same operator behind the 2015 Hola botnet scandal, under a different brand. The business model is straightforward: your home internet connection becomes a commercial proxy exit node. Bright Data’s third-party customers — web scrapers, marketing data firms, anyone willing to pay — route their traffic through your residential IP. Whatever they do online exits your house, attached to your name, on your bill.
If one of those customers is doing something abusive — credential stuffing, scraping copyrighted content, hitting geo-blocked services — the IP that gets logged, complained about, or sued is yours. Not Bright Data’s.
This program was fully installed on my laptop before I had ever touched the machine.
There’s also forensic evidence of a service named BVPNPreinstallMonitorService in the Windows event logs, with workflow stages internally labeled exec, windows_audit, oobe, and autostart. That language is consistent with Bright Data’s commercial OEM preinstall partner program — meaning the seller may have been running a paid pipeline. I can’t prove the contractual relationship from the laptop alone. I can prove the program ran, and I can prove when. The rest is inference.
Independent confirmation: Malwarebytes flagged 15 threats
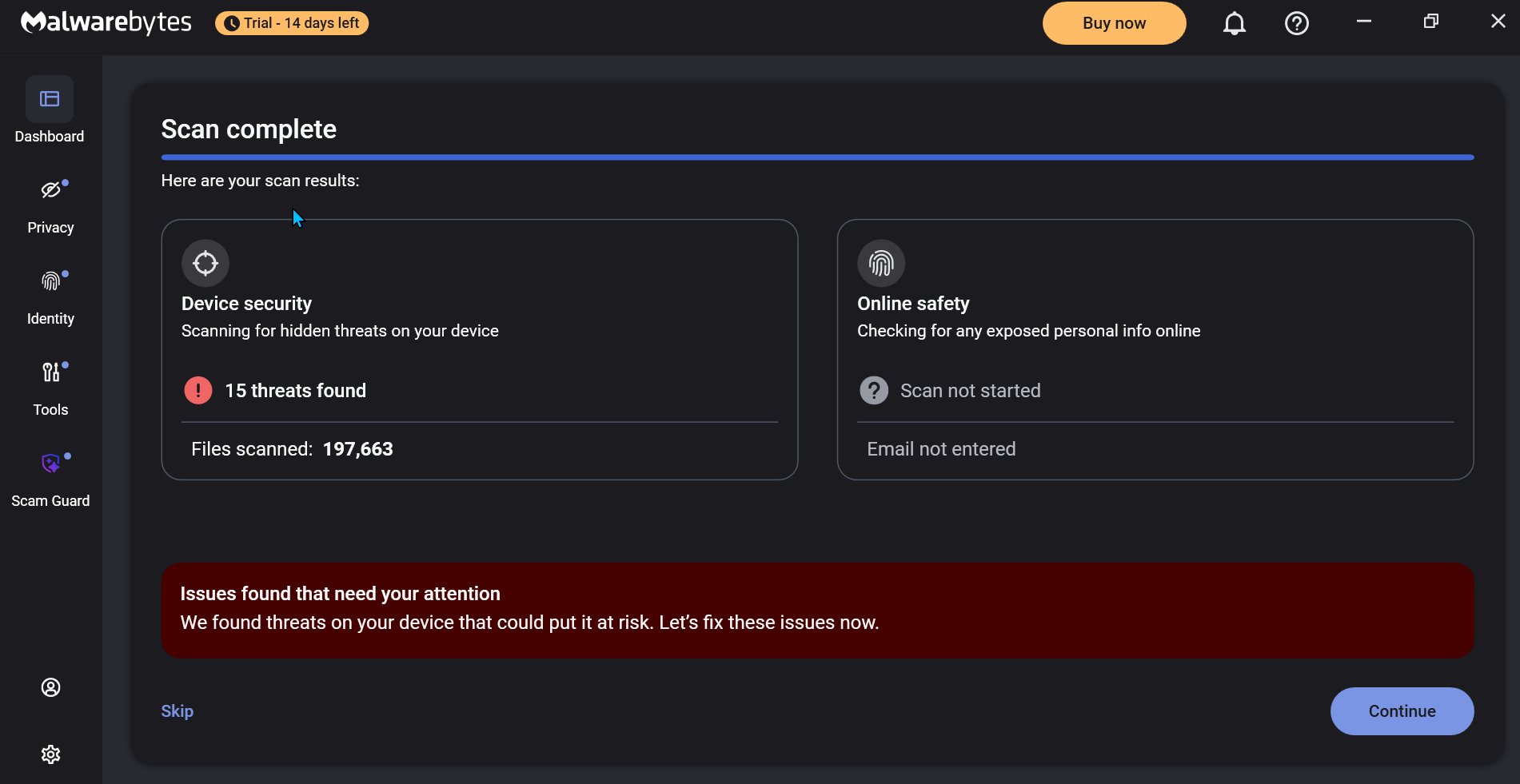
I’m not asking anyone to take my Prefetch analysis on faith. I ran a full scan with Malwarebytes — the industry-standard commercial scanner. It scanned 197,663 files and flagged 15 threats across three unwanted-program families, every one matching what the manual forensics had already pinned:
PUP.Optional.PCAppStorePUP.Optional.BrightData— fully installed program with Start Menu shortcut and uninstall registry entryPUP.Optional.VeryFast— a third unwanted family I hadn’t even spotted manually
Two independent forensic methods. Same conclusion.
The Amazon Renewed problem
Amazon’s Renewed program publishes specific quality standards. Renewed sellers are required to ship products that:
- Have a fresh OS install with no previous-user data
- Contain no preinstalled adware or unwanted third-party software
- Arrive in “as-new” condition
The seller did do the fresh OS install on February 3. That part of the program standard, they followed. Then — by the timestamps — they injected adware and a residential proxy onto the clean OS seven days later. That’s the program-standard violation. The “as-new condition” promise falls automatically once you accept that a clean Dell laptop and a Dell laptop with a residential proxy phoning home are not the same product.
The seller of record
Per the Amazon order detail page: ElectronicsBazaar Store, a doing-business-as name for Kay Kay Overseas Corporation. Kay Kay describes itself in its Amazon About-Seller blurb as a refurbisher of “premium and ’equal to new’ quality” PCs, and operates parallel storefronts on Amazon, eBay, and Newegg under the ElectronicsBazaar brand.
If their bench process produces this output once, it almost certainly produces it across an entire production batch. The Amazon listing showed over 100 units sold of this SKU from this seller. Every other customer who bought a Renewed laptop from Kay Kay in the same QA window may currently have Bright VPN running on their home network without knowing.
Where this stands now
A small-claims lawsuit has been filed and accepted by the court: Bowman v. Amazon.com Services LLC, Volusia County, Florida, Case No. 2026 17782 COCI. Filed May 6, 2026. Pretrial conference set for August 11, 2026. The filing is grounded in Florida consumer-protection law. Regulatory complaints with the Florida Attorney General and other agencies are next on the list.
Amazon’s Executive Customer Relations responded the same day, opening an internal ticket and routing the matter to their Legal Team. That correspondence is preserved as part of the case record.
This page will be updated as the case develops.
What to check if you bought from this seller
If you bought a laptop, desktop, or phone through Amazon Renewed in the last 12 months and you’ve seen unexpected popups, browser redirects, slow performance, or a “Bright VPN” entry in your installed apps list — don’t assume it’s a virus you picked up. Run these:
Settings → Apps → Installed apps. Sort by install date. Anything that says it was installed before your first power-on did not come from you. Screenshot it.
Run Malwarebytes (free version is fine). Save the report.
Open PowerShell as Administrator and run:
Get-ChildItem C:\Windows\Prefetch -Filter *.pf | Sort-Object CreationTime | Select-Object Name, CreationTime, LastWriteTimeAnything older than your first logon is preinstalled, not yours.
File an Amazon A-to-z claim under “item materially different from description.” You can request a partial refund — keep the device and get money back. Amazon does grant these in cases like this; most consumers don’t know to ask.
For a paper trail with teeth, file a BBB complaint against Amazon.com, Inc. (Seattle, WA) — not against the third-party seller. Frame it as Amazon’s failure to enforce its own Renewed program standards.
You can also email Amazon Executive Customer Relations at ecr@amazon.com (cc jeff@amazon.com) with the same evidence package — that path tends to get a real human at corporate to read it.
If you have screenshots showing the same BVPNPreinstallMonitorService or PC App Store install on your machine, contact Bowman Web Services. Your evidence helps build the pattern.
Update log
May 6, 2026 — Initial publication. Forensic evidence, Malwarebytes scan, and Amazon order details documented above.
May 6, 2026 — BBB complaint filed against Amazon.com, Inc. naming ElectronicsBazaar Store (Kay Kay Overseas Corporation) as the seller of record. Filing identifies failure to enforce Renewed program standards.
May 6, 2026 (evening) — Lawsuit filed. Bowman v. Amazon.com Services LLC, Volusia County, Florida, Case No. 2026 17782 COCI (UCN 642026SC017782XXXACI), Filing #247643371. Filed and accepted at 7:04 PM ET. Pretrial conference set August 11, 2026. Summons issued. Litigation hold request transmitted to Amazon Executive Customer Relations.
May 6, 2026 — Amazon Executive Customer Relations response received confirming an internal ticket and Legal Team referral.
May 8, 2026 — Amazon blocked one-star review of the same listing. Review submitted 5/8/2026 9:24 AM ET (Amazon Reference R9NRAS3H4BZB8), titled “Spyware or Adware Injected In laptop,” describing the same forensic findings documented above. Takedown email cites “community guidelines.” Screenshot of takedown email retained as evidence of suppressed consumer warning.
This page will be updated with each material development.
— Tommy Bowman, Bowman Web Services LLC, Daytona Beach, Florida
Nothing on this page is a legal accusation. Every factual claim above is documented with timestamps, file paths, and tool output that anyone can independently verify on the same laptop. The word “alleged” is used where a legal element of fraud or deception is implied but has not been adjudicated.